Blog Article
Why Static Advance Reports Aren't Enough
Advance reports are essential. But the operating environment isn't static. Between production and principal arrival, the threat surface shifts. Here's how to close that gap.
Category
Intelligence
Author
Capxel Security Research
Reading Time
3 min read
Author
Capxel Security Research
Capxel Security editorial briefings
Published March 20, 2026 with a reading layout optimized for leaders, analysts, and operators.
The advance report is the foundation. It is not the ceiling.
Every executive protection detail, corporate travel security program, and event security operation depends on advance work. The advance report maps the terrain: hospitals, police stations, venues, ingress and egress, choke points, route exposure.
That report is critical. It is also frozen the moment it is produced.
The operating environment moves after the report is written.
A protest is organized 48 hours before arrival. A severe weather system shifts the forecast window. A crime spike emerges in the hotel corridor. A large concert floods the area with 30,000 people the night before a meeting. A construction detour reroutes the primary evacuation route.
None of that appears in the advance report. The report was accurate when it was produced. The operating environment changed.
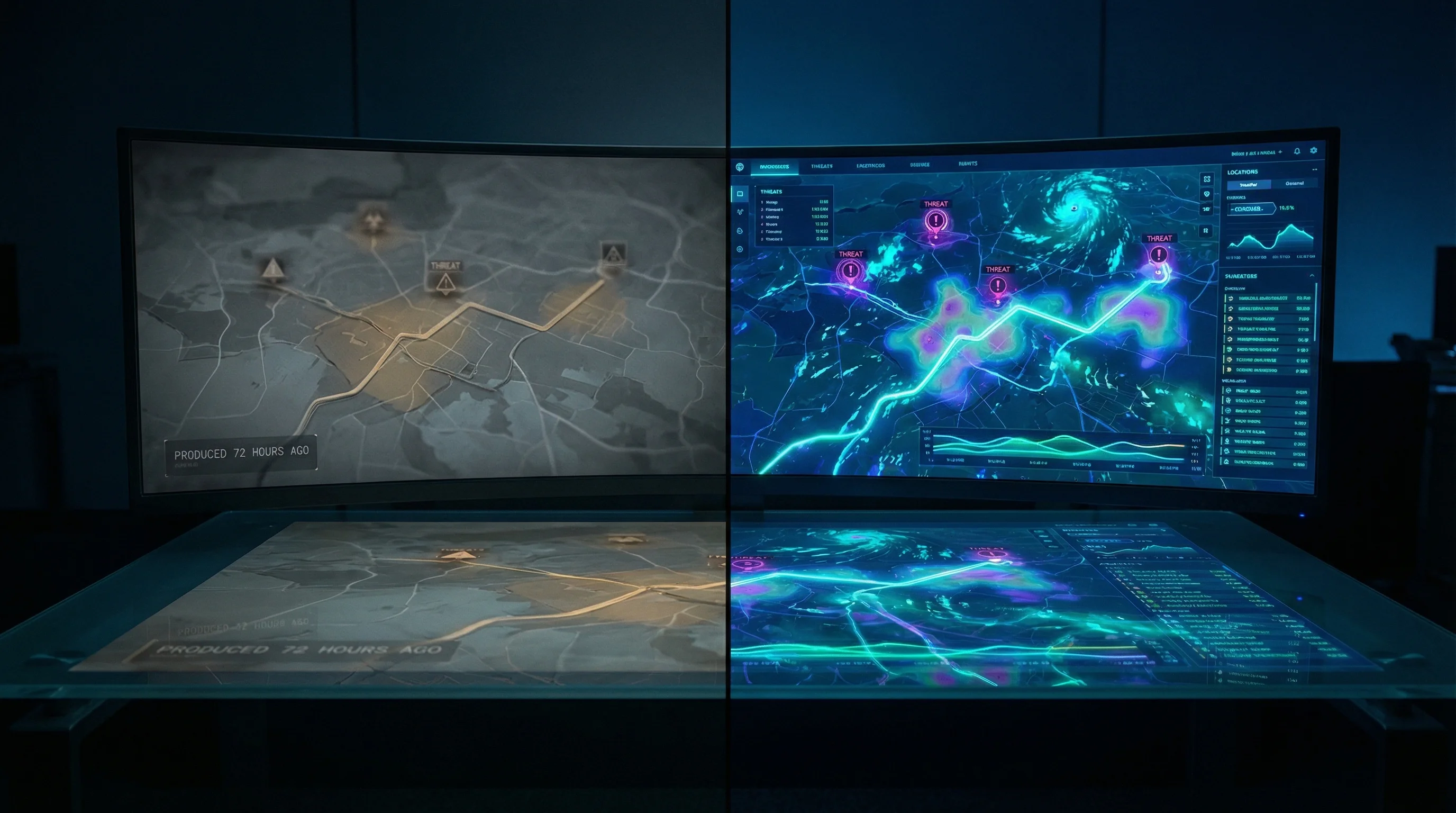
The gap between static and temporal intelligence.
Traditional advance reports answer: what is at this location?
That is necessary but insufficient. Operators also need to know: what is happening at this location right now, and what is about to happen?
This is the distinction between spatial intelligence and temporal intelligence. Spatial intelligence maps the environment. Temporal intelligence monitors the environment across a time window. Both are required for complete pre-arrival preparation.
What temporal intelligence looks like in practice.
Consider a three-day executive detail in Miami:
- Day 1: The advance report identifies four hospitals within 5 miles, two police precincts, venue layout, primary and contingency routes. This is spatial.
- Day 1 also needs: 23 violent crime incidents in the last 30 days within the operational radius. A permitted protest march planned for Day 2 along a route that intersects the primary motorcade path. Thunderstorm warnings for Day 3 with 40mph gusts. Three large events at nearby venues that will cause significant traffic density on Day 2 evening.
The spatial data is the map. The temporal data is the weather. You need both to operate.
The Intelligence Brief closes this gap.
Capxel Security built the Intelligence Brief as the temporal companion to every Advance Report. The Intelligence Brief sweeps 8 intelligence layers — crime patterns, civil unrest, severe weather, local events, infrastructure disruptions, travel advisories, medical infrastructure, and local media pulse — and delivers a branded, decision-ready brief alongside the advance report.
The result: operators arrive with both the map and the weather. The advance report tells them what is there. The Intelligence Brief tells them what is happening.
Static is not a failure. It is incomplete.
The advance report is not wrong. It is essential. But treating it as the complete picture creates blind spots in exactly the operational windows where blind spots are most dangerous: the 24-72 hours before principal arrival.
If your advance work stops at spatial intelligence, you are missing the temporal layer that turns a good report into a complete operational picture.
Related Articles
Keep the briefing window open.
More Capxel Security analysis on AI-native threats, enterprise controls, and operator-grade intelligence workflows.
The $100K Problem: Enterprise Threat Intelligence vs. Mission-Specific Intelligence
Enterprise threat platforms cost $100K+ per year and monitor everything, everywhere. Most security teams need intelligence for specific destinations, specific dates, and specific operational windows. The market has a gap.
Continue ReadingWhat Goes Into an Intelligence Brief
Eight intelligence layers, eleven data sources, one branded brief. Here's what the Intelligence Brief actually sweeps — and why each layer matters for operational awareness.
Continue ReadingYour Browser's AI Assistant Is Now an Attack Surface
CVE-2026-0628 let malicious Chrome extensions hijack Gemini's AI panel — accessing cameras, microphones, and local files without user consent. This isn't a browser bug. It's a preview of the AI security era.
Continue ReadingNewsletter
Want more briefings in this format?
Subscribe for new Capxel Security analysis on agentic security, enterprise controls, and premium intelligence workflows.
Work With Capxel Security
Need a product briefing after reading the analysis?
Capxel Security can route you into DOSXIER, Advance Reports, or an AgentSec evaluation when you're ready for a deeper conversation.