Blog
Field notes on threat intelligence and agentic defense.
Capxel Security publishes briefings on agentic threats, enterprise controls, and the operational realities behind decision-ready intelligence work.
Agentic threats
How AI-native attack surfaces evolve across prompts, tools, runtime behavior, and trust boundaries.
Operator workflows
What premium investigative and protective workflows can teach modern security product design.
Enterprise controls
Control concepts for leaders deploying copilots, workflow agents, and AI-enabled business systems.
Signal
DOSXIER delivery window
Signal
Intelligence categories
Signal
AgentSec control surfaces
Signal
Mission-built product lines
Featured Briefing
Briefings built for decisive security reading.
Capxel Security articles are designed to feel as intentional and high-trust as the platform itself.
The $100K Problem: Enterprise Threat Intelligence vs. Mission-Specific Intelligence
Enterprise threat platforms cost $100K+ per year and monitor everything, everywhere. Most security teams need intelligence for specific destinations, specific dates, and specific operational windows. The market has a gap.
Author
Capxel Security Research
Why it matters
Reading posture
Elite, precise, and designed to be kept open during planning.
All Articles
Briefings shaped by field credibility and operational thinking.
Every article is built for security leaders, operators, and analysts who need precise, actionable intelligence — not marketing content.

What Goes Into an Intelligence Brief
Eight intelligence layers, eleven data sources, one branded brief. Here's what the Intelligence Brief actually sweeps — and why each layer matters for operational awareness.
Capxel Security Research
March 20, 2026
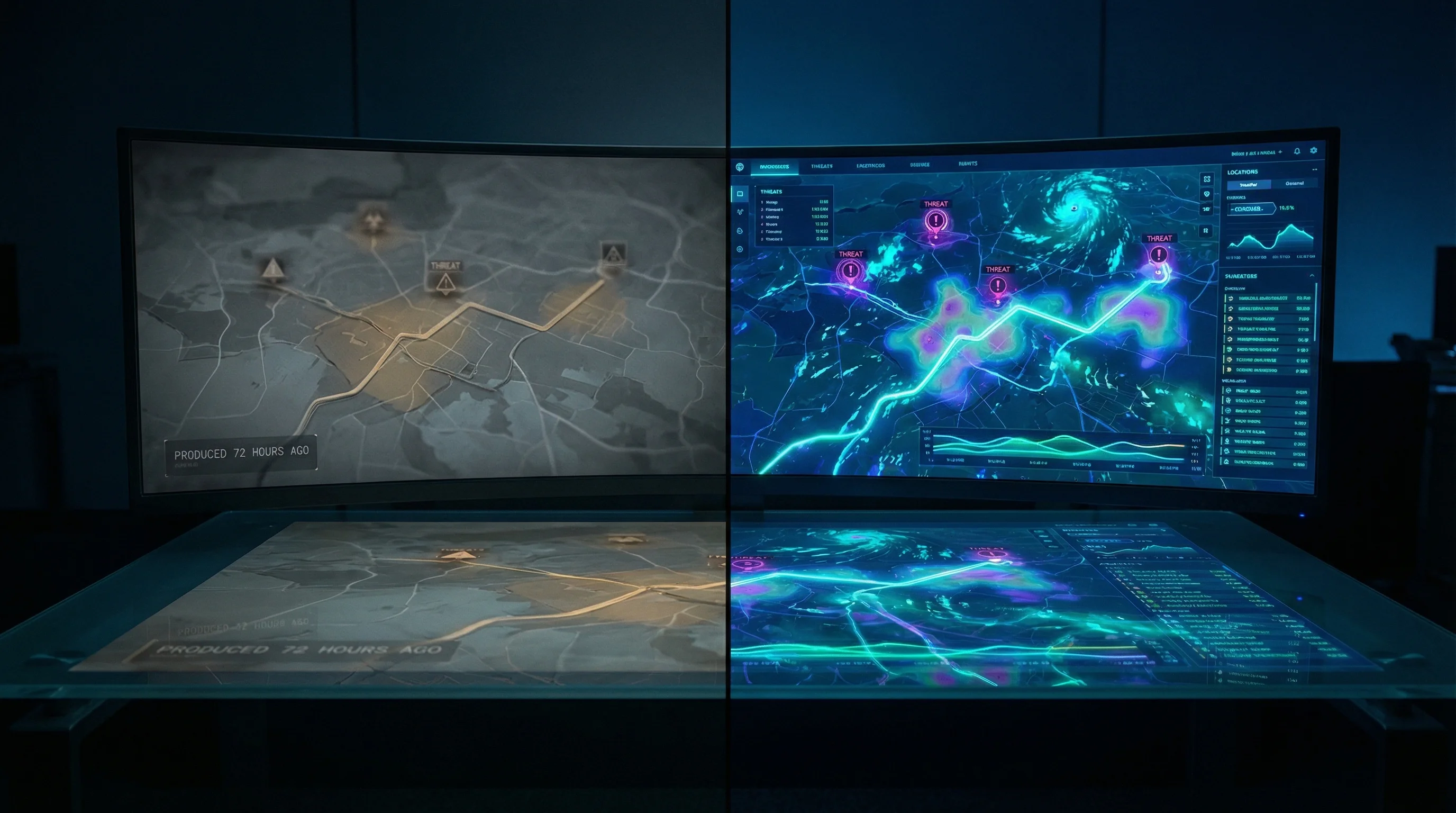
Why Static Advance Reports Aren't Enough
Advance reports are essential. But the operating environment isn't static. Between production and principal arrival, the threat surface shifts. Here's how to close that gap.
Capxel Security Research
March 20, 2026

Your Browser's AI Assistant Is Now an Attack Surface
CVE-2026-0628 let malicious Chrome extensions hijack Gemini's AI panel — accessing cameras, microphones, and local files without user consent. This isn't a browser bug. It's a preview of the AI security era.
Capxel Security Research
March 12, 2026

Microsoft Just Proved Why AI Agent Security Can't Wait
Microsoft's Agent 365 announcement validates what we've been building: AI agents are a security surface, and nobody is adequately monitoring them. Here's what they got right — and the critical gaps they didn't address.
Capxel Security Research
March 12, 2026

Your Browser's AI Assistant Is Now a Security Surface
CVE-2026-0628 exposed a high-severity flaw in Chrome's Gemini AI panel that let malicious extensions hijack cameras, microphones, and local files without asking permission. This is the new threat model nobody is ready for.
Capxel Security Research
March 12, 2026

GPT-5.4's Native Computer Use: What Security Teams Need to Know Now
OpenAI's latest model can control computers autonomously — beating human benchmarks. Here's why that changes the security equation for every organization deploying AI agents.
Capxel Security Research
March 6, 2026

Reclaim Security Just Raised $26M for 'Agentic Remediation.' Here's What That Validates.
A $26M Series A for automated security remediation confirms the market is moving. But closing the remediation gap is Layer 2. The real opportunity is Layer 3.
Capxel Security Research
March 6, 2026

Agent Hijacking: The New Insider Threat No One's Talking About
When your AI agent has more access than your employees, the threat model changes completely. Compromised agents don't just leak data — they take actions.
Capxel Security Research
March 5, 2026

Why 24 Hours Changes Everything: The Case Against 14-Day Intelligence
In an industry where threat assessments can take up to two weeks, DOSXIER's 24-hour turnaround isn't just faster — it's a fundamentally different product.
Capxel Security Research
March 4, 2026

DOSXIER: 24-Hour Intelligence in a 2-Week Industry
Licensed security providers do not have two weeks to wait. DOSXIER compresses investigative turnaround into a single operational day.
Capxel Security Research
February 22, 2026

Why AI Agents Need Security Clearance
Agentic systems should not be trusted by default. They need scoped authority, monitored behavior, and a real trust model.
Capxel Security Research
February 10, 2026

The Rise of Agentic Threats: What Your Business Needs to Know
As businesses deploy more autonomous workflows, the threat model changes from app misuse to agent manipulation, trust abuse, and runtime compromise.
Capxel Security Research
January 28, 2026
Editorial Desk
Authors and themes aligned with Capxel Security's point of view.
The editorial desk highlights the people and domains behind the analysis so the voice stays consistent with the operating standard.
Capxel Security Research
Contributes analysis on agentic security posture.
Briefings
Short, decisive reads for operators and executives.
Controls
Practical perspectives on securing AI-native systems.
Workflows
Lessons from licensed-provider operations and field realities.
Context
Why the security landscape is shifting under the agentic era.
Newsletter
Intelligence briefings delivered to your inbox.
Subscribe for new Capxel Security analysis on agentic threats, enterprise defense, and operator-grade intelligence workflows.
Beyond The Blog
Need product access instead of just analysis?
Capxel Security can route you into DOSXIER, Advance Reports, or an AgentSec briefing when you're ready to move from reading to deployment.